This post provides detailed analysis and an exploit achieving remote code execution for CVE-2020-10882, which was used at Pwn2Own 2019, on the TP-Link Archer C7. This bug was found by Pedro Ribeiro and Radek Domanski of Team Flashback.
This vulnerability allows network-adjacent attackers to execute arbitrary code on affected installations of TP-Link Archer A7 AC1750 routers. Authentication is not required to exploit this vulnerability.
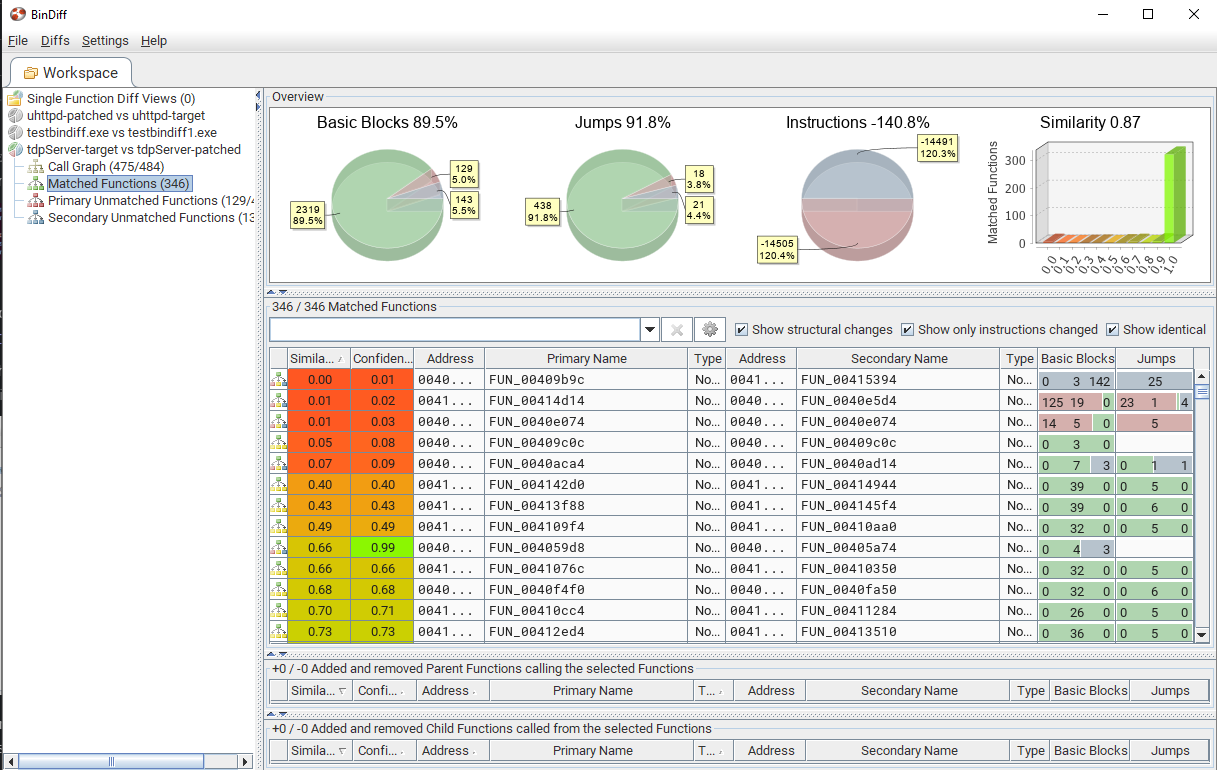
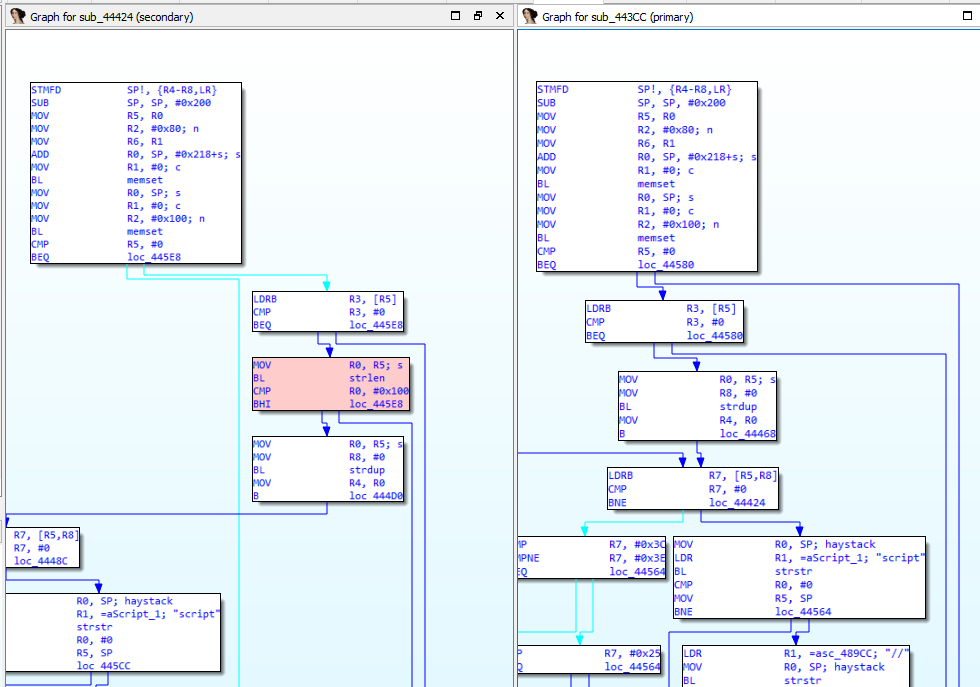
The specific flaw exists within the tdpServer service, which listens on UDP port 20002 by default. When parsing the slave_mac parameter, the process does not properly validate a user-supplied string before using it to execute a system call. An attacker can leverage this vulnerability to execute code in the context of the root user.
This blog post shows the effort to find the root cause, then understanding the packet structure, triggering the command injection bug and getting remote code execution.
Click here to get to the blogpost.